// MALWARE INTELLIGENCE
SigmaWare Stealer
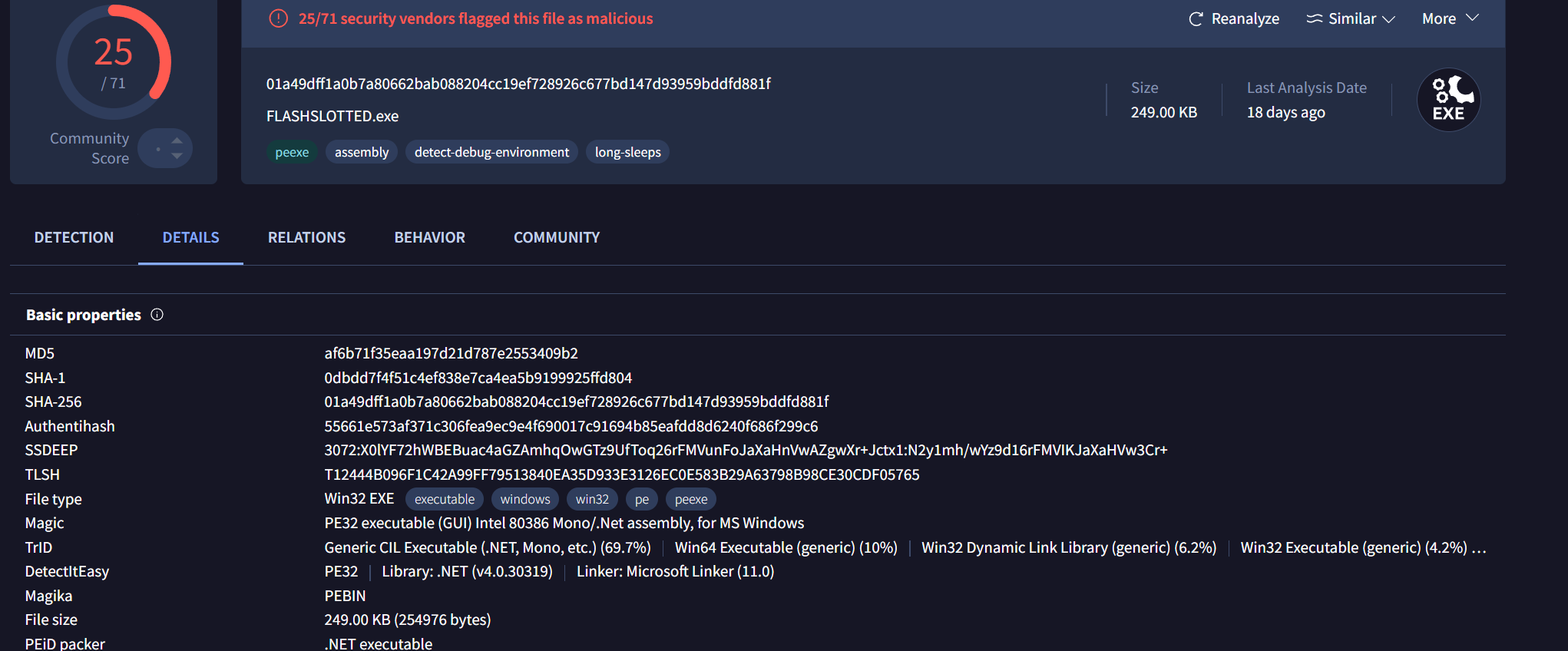
Investigation of suspicious samples on VirusTotal revealed multiple malicious files communicating with infrastructure linked to SigmaWare Stealer, a commercial information stealer distributed within underground communities.
Static and behavioral analysis confirms credential theft, screen capture, and surveillance capabilities matching SigmaWare’s advertised features.
VirusTotal Sample Evidence
Basic sample information observed in VirusTotal:
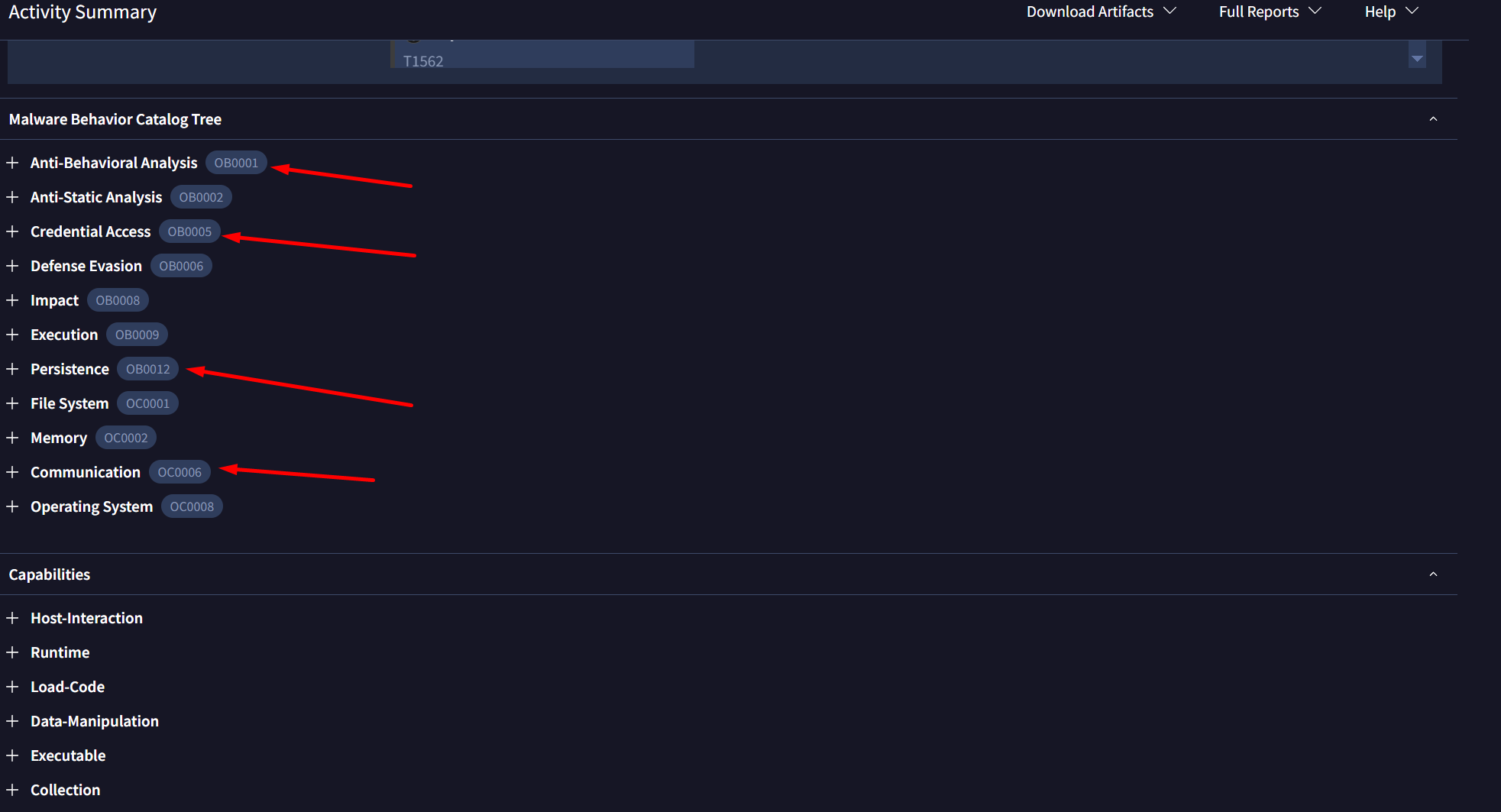
Behavioral execution showing stealer activities:
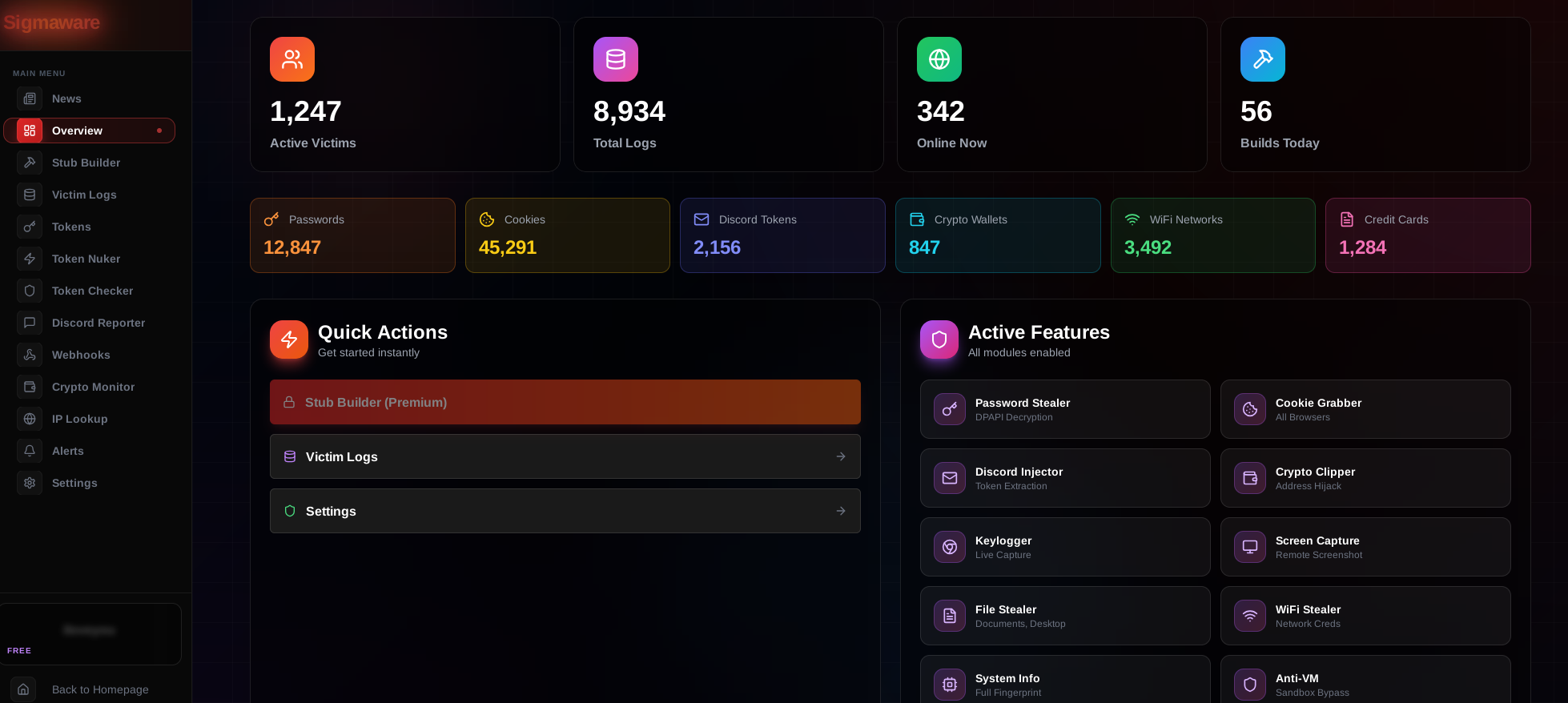
Advertised Capabilities
The malware dashboard advertises capabilities including:
- Live screen capture
- Remote screenshots
- File theft
- Network credential stealing
- Anti-VM and sandbox bypass
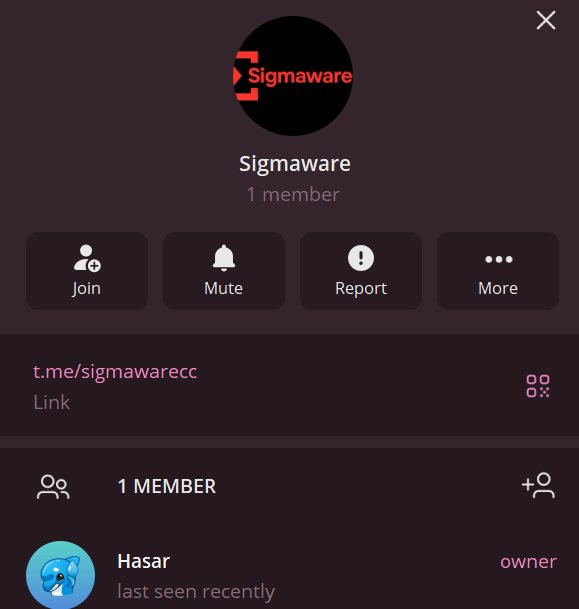
Operator Attribution
The operation appears linked to underground actor hasar0001, active on cybercrime forums and marketplaces.
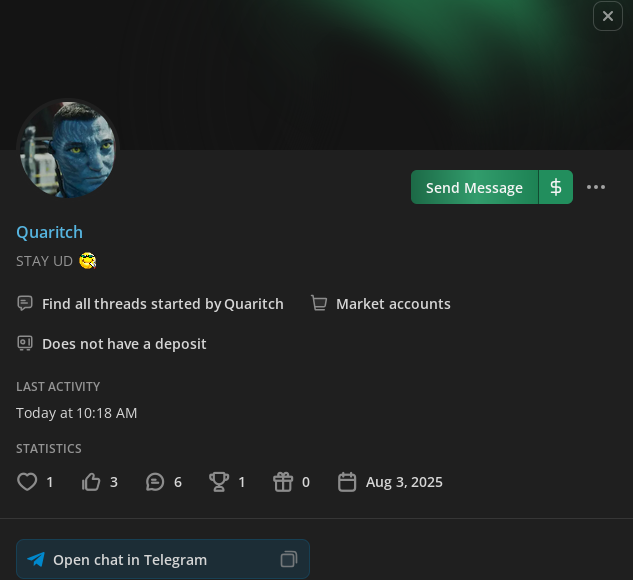
Telegram infrastructure used for communication:
https://t.me/sigmawarecc
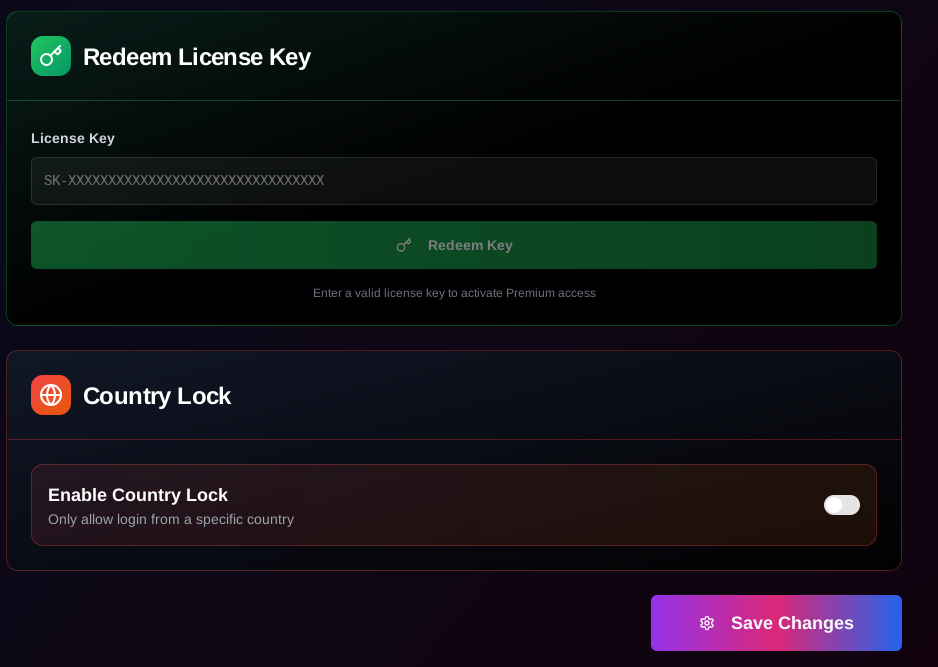
Panel Country Lock Feature
User of Sigmaware can restrict panel login to selected countries.
Indicators of Compromise
3d81d7c34040cf7eef01263d38d819331dc717b377c2b590b1538cdb25c7404e
e978a9f59e82c82775c0dd4da03971396d782c5cd9047b15228a458cc42b70b2
a8ae3c5ecaf6e261d4a46ec30ea88ee72b8a81f83440f73cd88a3a5fbf6c102f
Conclusion
SigmaWare operates as a commercial stealer platform providing credential theft and surveillance functionality. Observed telemetry and OSINT correlations indicate active underground distribution.