Nexus RAT
RAT Analysis
Executive Summary
This analysis identified a sophisticated Android Banking Trojan with full Remote Access Trojan (RAT) functionality targeting Russian banking customers, primarily Alfa-Bank users.
- Real-time remote screen control via VNC
- Accessibility-based keylogging
- SMS interception for OTP theft
- Native encrypted C2 infrastructure
Threat Level: HIGH
Sample Information
| Attribute | Value |
|---|---|
| Package Name | ru.y34tuy.t8595 |
| Disguise | Fake Device Manager |
| Native Library | libsysruntime.so |
| C2 Protocol | HTTPS REST + WebSocket |
Malicious Capabilities
- Remote VNC control of infected device
- Keylogging via Accessibility Service
- SMS interception and sending
- Overlay phishing attacks on banking apps
- Clipboard and notification theft
- USSD execution for fraud
- Device admin persistence
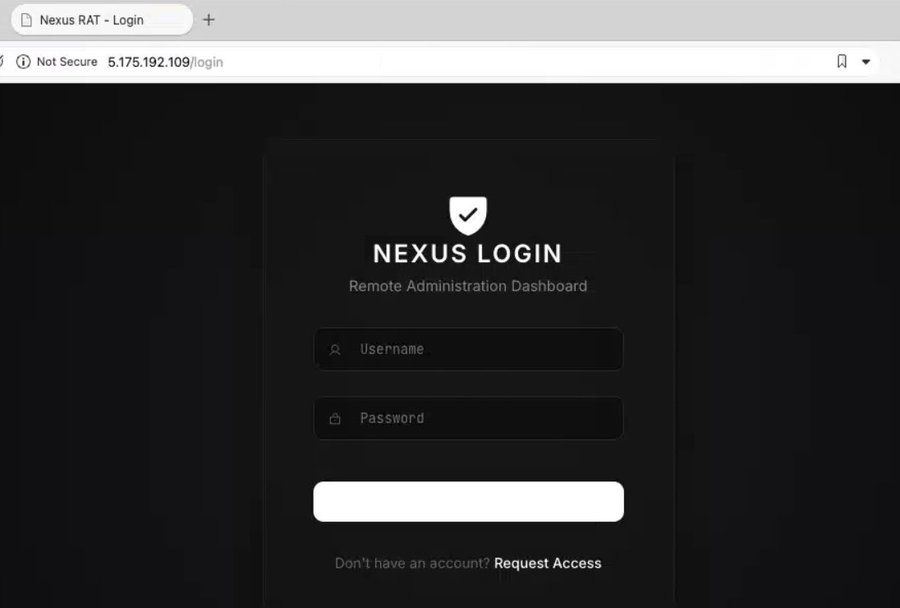
C2 Infrastructure
| Endpoint | Purpose |
|---|---|
| /api/v1/sync/init | Bot registration |
| /api/v1/sync/status | Heartbeat beacon |
| /api/v1/sync/config/{id} | Command retrieval |
| /api/v1/vnc/device/{id} | Live remote control |
Obfuscation Techniques
- XOR rolling encryption for strings
- Native encrypted C2 servers
- ProGuard obfuscation
- Encrypted runtime configuration
Indicators of Compromise
Package: ru.y34tuy.t8595
5.175.221.21:5000
6d8e017c4e80db7326d1f9d387f6890ae4aa7170274d277db1f2f972254bf1ba
70473a023fd78ae846f7e002a0952dce63ac8a7801d13ad81fbd6d228df51ada
95.168.134.12:5000
5.175.192.109:80
5.175.221.21:5000
6d8e017c4e80db7326d1f9d387f6890ae4aa7170274d277db1f2f972254bf1ba
70473a023fd78ae846f7e002a0952dce63ac8a7801d13ad81fbd6d228df51ada
95.168.134.12:5000
5.175.192.109:80
Persistence Mechanisms
- BOOT_COMPLETED receiver
- Accessibility Service persistence
- Device Admin privilege abuse
- Foreground services
- AlarmManager restart logic
Data Exfiltration
Device model
Android version
SIM operator
Phone numbers
Installed banking apps
Clipboard data
SMS messages
Android version
SIM operator
Phone numbers
Installed banking apps
Clipboard data
SMS messages
MITRE ATT&CK Mapping
| Technique | Description |
|---|---|
| T1417 | Input capture via keylogging |
| T1412 | SMS interception |
| T1406 | Obfuscated files |
| T1481 | C2 via web service |
Detection Recommendations
- Monitor /api/v1/sync/* traffic
- Flag Accessibility + SMS permissions
- Detect MediaProjection abuse
- Block suspicious WebSocket connections
Conclusion
This malware represents a highly capable Android banking trojan designed for credential theft, remote device control, and financial fraud. The use of native encryption, VNC access, and persistent C2 communication demonstrates a mature and professionally developed threat.