// RANSOMWARE INTELLIGENCE
CipherForce ransomware
A security researcher known as Bitshadow recently posted
about new ransomware named
CipherForce Following this disclosure, I conducted independent hunting and identified
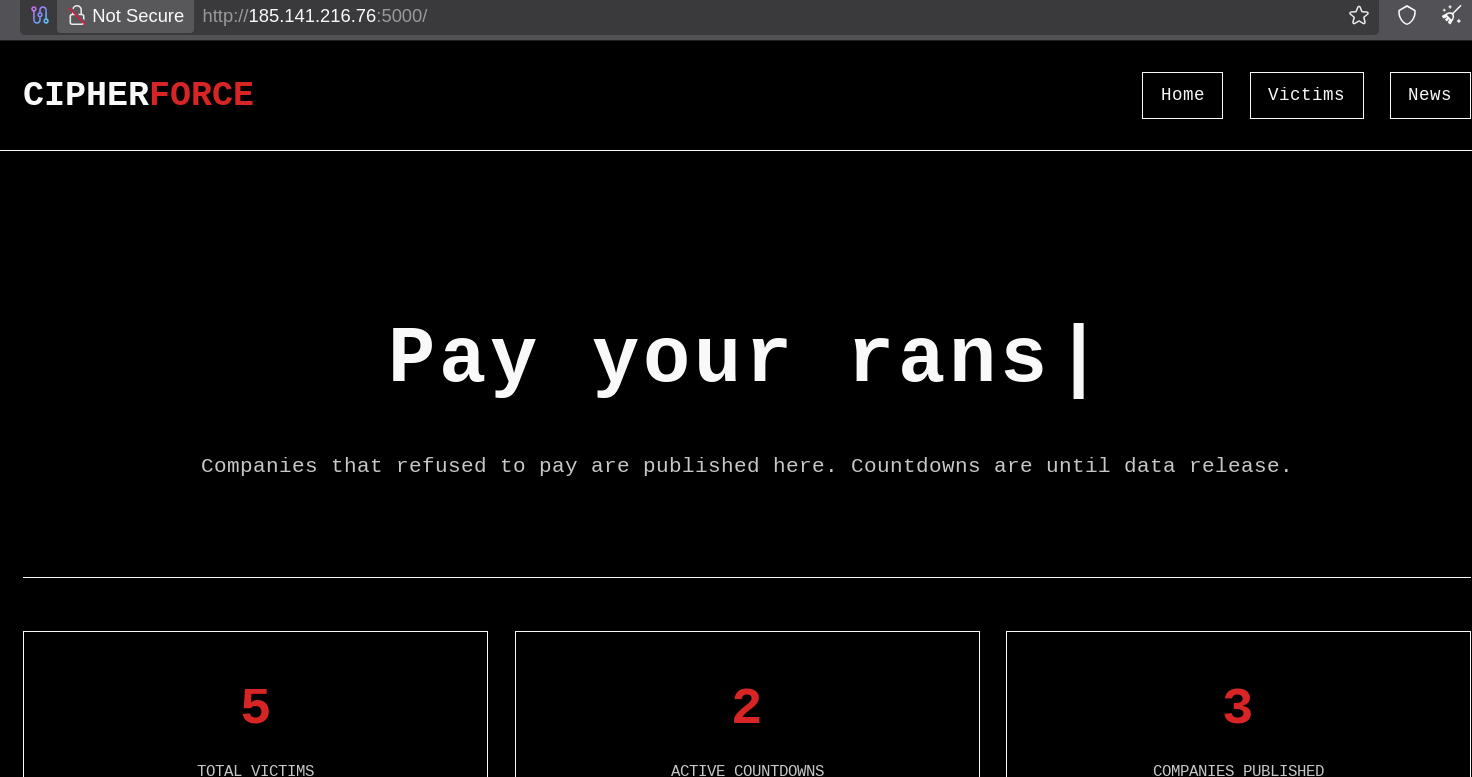
what appears to be the group’s affiliate panel and leak infrastructure at 185.141.216.76.
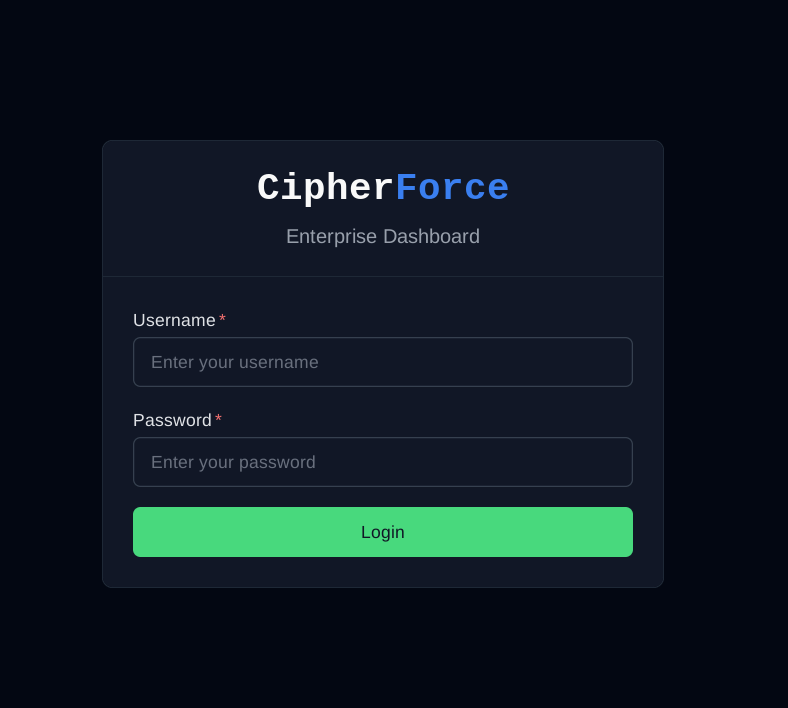
The ransomware’s affiliate dashboard is exposed on port 8000, while port 5000 hosts the public-facing blog where victim data is listed. At the time of analysis,
the leak site shows five confirmed victims, with countdown timers actively running for two, indicating imminent data release.
The affiliate dashboard itself is notably mature and feature-rich, suggesting an organized and scalable RaaS (Ransomware-as-a-Service) operation. Observed modules include:
- Payload and builder management (Windows & Linux)
- Exfiltration and beacon tracking
- AV and environment checks
- Network and infrastructure visibility
- Earnings, affiliate statistics, and master-level controls
/builds
/exfils
/beacons
/av-check
/db-build
/earnings
/networks
/s3-build
/tickets
/advanced-build
/master/earnings
/master/companies
/linux-advanced-build
The presence of advanced build pipelines, earnings management, and centralized “master” sections strongly indicates an active recruitment model
and a well-structured backend rather than an experimental or short-lived threat.
For those unfamiliar with the group, the operators previously identified themselves as TeamPCP or Shellforce, claiming prior involvement in data leaks and malware development activities.
CipherForce appears to be their newer initiative, positioned as a ransomware project aimed at recruiting affiliates and expanding operations.
According to statements published in their “About” section, the team suggests prior activity in the ransomware space
and indicates plans to begin publishing victim companies under the CipherForce banner in the near future.